AI Use Cases
Why AI in Cybersecurity is the Foundation of a $51B Market in 2026
Explore AI in Cybersecurity, from threat detection to future trends. Learn how AI tools protect systems and empower modern security teams.
Share
The cybersecurity industry is evolving faster than ever, and relying on outdated defense tactics is no longer a viable option. As cyber criminals become more advanced, organizations need smarter, faster, and more adaptive protection. That is exactly where AI in cybersecurity is making its mark.
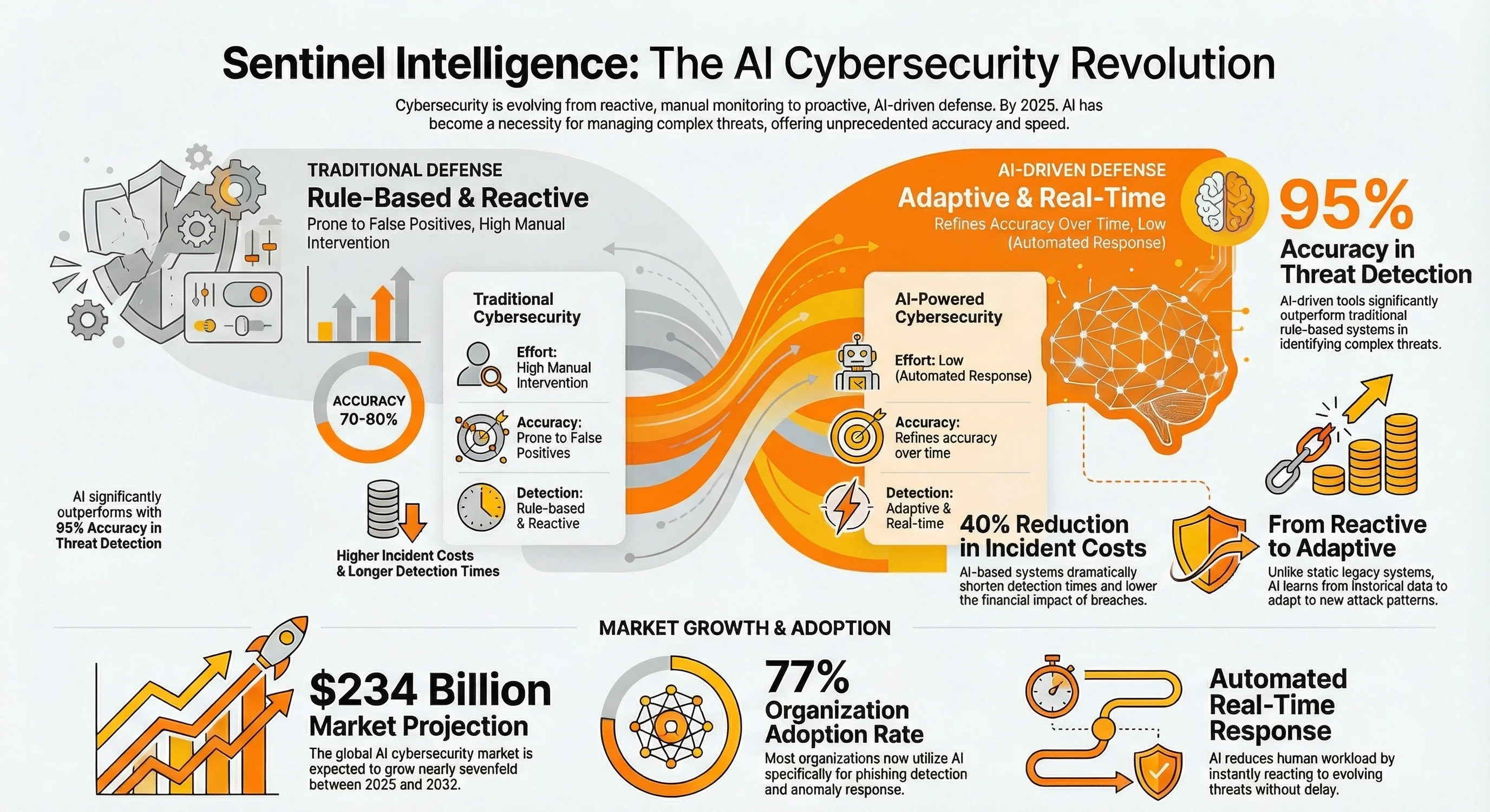
The global AI in cybersecurity market is forecast to expand from $34 billion in 2025 to $234 billion by 2032
Artificial intelligence is not just improving cybersecurity—it is redefining it. From analyzing vast streams of network traffic to identifying patterns in user behavior, AI brings speed, scale, and precision that human analysts alone cannot match.
Security teams are now using AI-powered systems to detect cyber threats in real time, respond instantly, and even predict attacks before they happen.
Nearly 7 in 10 organizations now use AI in their cyber defenses, with threat detection being the most common application
This article explores how AI is transforming cybersecurity today. We will look at real use cases, powerful AI tools making a difference, and the exciting future of intelligent threat prevention. If you want to stay ahead, this is the place to start.
What Is AI in Cybersecurity and Why Does It Matter?
AI in cybersecurity is not just a technical upgrade; it is a necessary evolution. As cyber threats become increasingly complex and relentless, artificial intelligence provides a more innovative, faster way to protect sensitive data, digital assets, and entire infrastructures.
In 2025, AI‑driven threat detection tools are reported to improve detection accuracy by up to 95% compared to traditional approaches, meaning fewer threats slip through unnoticed
AI systems help security teams detect anomalies, analyze vast amounts of data, and respond to threats in real time. But it is not only about speed. AI brings adaptability. It learns from historical data and adapts to new attack patterns without constant human intervention.
For organizations that face daily phishing attacks, ransomware, or data breaches, AI-powered cybersecurity solutions can mean the difference between proactive protection and reactive damage control.
The global AI in cybersecurity market was valued at around USD 34.1 billion in 2025 and is projected to grow to over USD 234 billion by 2032, showing how widely organizations are investing in AI‑based defenses.
To understand why AI matters in this field, let’s break down its core role, how it differs from traditional systems, and what makes up an effective AI-powered cybersecurity approach.
Understanding the Role of AI in Cyber Defense
AI plays a crucial role in strengthening cyber defense strategies. It enables security teams to go beyond manual monitoring by automating threat detection, analyzing user behavior, and predicting potential threats before they escalate.
Around 77% of organizations now use AI technology in cybersecurity, especially for phishing detection and anomaly response
Here is a breakdown of AI’s core responsibilities in cyber defense:
| AI Role | Function |
|---|---|
| Threat Detection | Identifies unusual patterns in network traffic and flags potential threats |
| Behavioral Analytics | Tracks user behavior to detect suspicious activities |
| Real-Time Response | Enables instant reaction to evolving threats without delay |
| Predictive Threat Intelligence | Uses historical data to anticipate future attacks |
| Automation of Routine Security Tasks | Reduces human workload and improves response time |
How AI Differs from Traditional Cybersecurity Methods
Traditional cybersecurity tools rely heavily on predefined rules and human intervention. AI, on the other hand, adapts in real time, using machine learning algorithms to stay ahead of emerging threats and reduce false positives.
Modern AI tools are reported to improve threat detection by about 60% compared to legacy systems, enabling organizations to identify and respond to attacks much faster.
Let’s compare AI-based and traditional cybersecurity approaches:
| Aspect | Traditional Cybersecurity | AI-Powered Cybersecurity |
|---|---|---|
| Threat Detection | Rule-based, reactive | Adaptive, real-time analysis |
| Human Involvement | High (manual review and intervention) | Low (automated response with human oversight when needed) |
| Scalability | Limited | High, especially with large datasets and growing networks |
| Accuracy | Prone to false positives | Learns and refines accuracy over time |
| Handling New Threats | Slow to adapt | Continuously evolves using AI models |
Key Components of AI-Powered Cybersecurity Systems
AI-powered systems are built with multiple intelligent components that work together to enhance security measures, identify vulnerabilities, and enable proactive defense strategies.
AI‑based systems reduce breach detection time dramatically. In real deployments, AI techniques can shorten the time to detect a cyber threat by hundreds of days and lower incident costs by up to 40 % versus legacy approaches.
Here are the key building blocks:
| Component | Purpose |
|---|---|
| Machine Learning Algorithms | Analyze patterns in historical data and improve accuracy over time |
| Natural Language Processing (NLP) | Detects phishing or social engineering attempts through communication analysis |
| Behavioral Analytics Engine | Monitors user behavior for anomalies |
| Threat Intelligence Integration | Feeds AI with data on emerging threats and known attack vectors |
| Automation Framework | Responds to security incidents without constant human intervention |
| Continuous Learning Module | Refines detection capabilities based on new inputs and security incident data |
How Does AI Detect and Prevent Cyber Threats?
Instead of waiting for a breach to occur, AI systems actively monitor for potential threats, flag risks, and help security teams respond faster than ever before.
These capabilities rely on a powerful combination of machine learning, natural language processing, and behavioral analytics—each working together to recognize, stop, and even predict cyber threats.
According to industry data, around 60 % of organizations now use AI to identify patterns that signal impending threats, helping them flag risks before they fully materialize.
Real-Time Threat Detection with AI Tools
AI tools scan network traffic in real time, uncovering threats that might bypass traditional systems.
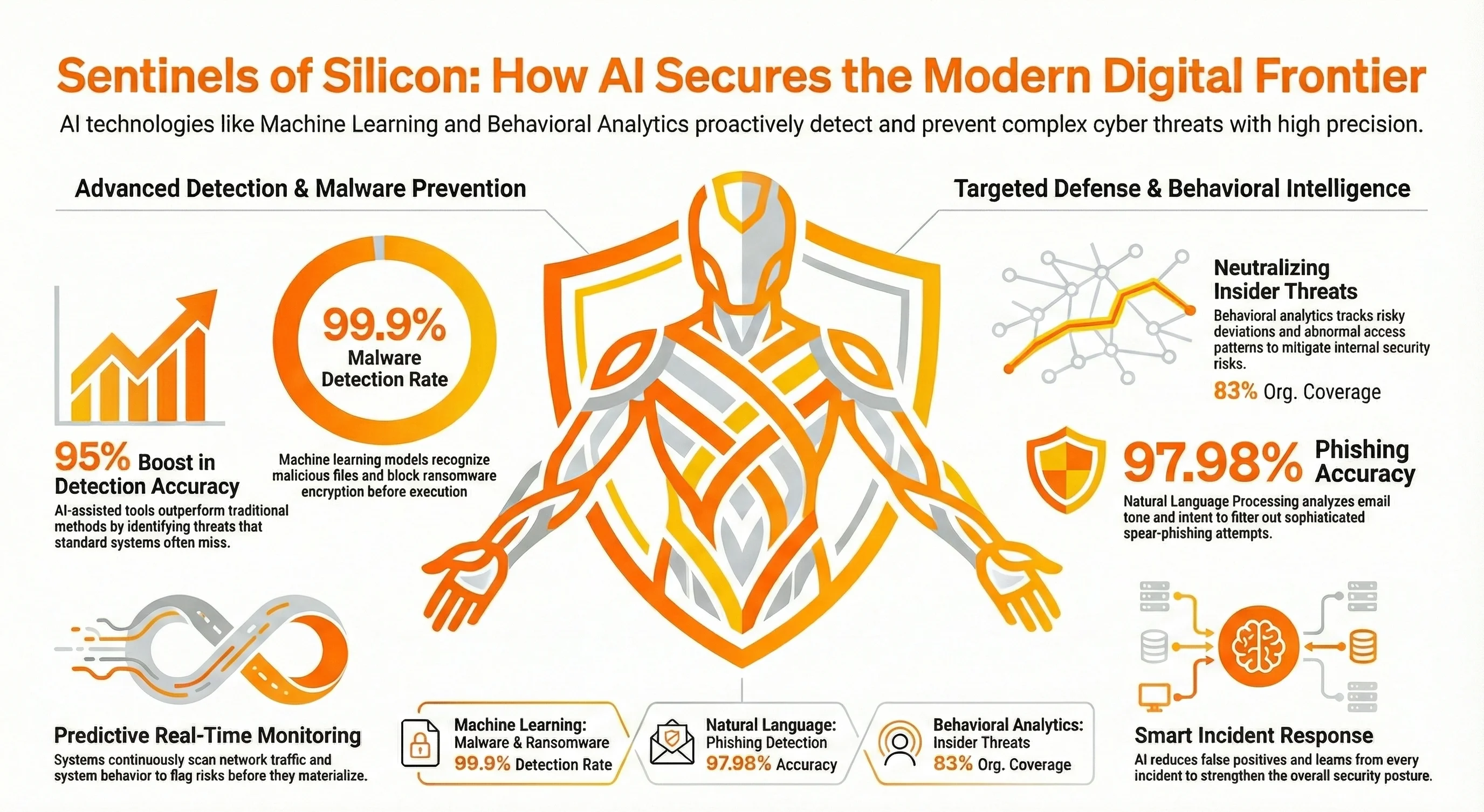
Organizations using AI‑assisted threat detection report that it can improve threat detection accuracy by up to 95 % compared with traditional methods.
How does it work?
- Continuously monitor for anomalies in system behavior or user activity
- Quickly analyze security logs to spot patterns linked to known cyber attacks
- Reduce false positives through refined, adaptive learning
- Alert security professionals immediately for faster intervention
- Strengthen the overall security posture by learning from each incident
Machine Learning for Malware and Ransomware Prevention
Machine learning brings a predictive edge to malware detection that static rules cannot match.
ML‑based ransomware and malware detectors have achieved very high accuracy in real tests, with some models reporting detection rates of up to 99.9 % while keeping false positives extremely low.
How does it work?
- Trains on historical data to recognize malicious files
- Detects malware and phishing detection attempts, even those previously
- Flag unauthorized access attempts based on activity spikes
- Supports endpoint security by scanning devices for potential threats
- Blocks ransomware by identifying encryption behavior before execution
Behavioral Analytics for Insider Threat Detection
Insider threats are hard to catch, but AI's ability to monitor behavior changes makes it possible.
According to recent industry reports, 83 % of organizations reported at least one insider threat incident in the past year. That underlines why proactive, behavior‑based detection has become essential for modern cybersecurity.
How does it work?
- Tracks user behavior to detect risky deviations
- Flags abnormal access patterns to sensitive data
- Correlates access logs and system usage across departments
- Helps reduce reliance on manual reviews by security professionals
- Enhances visibility into internal security risks and misuse
Natural Language Processing in Phishing Detection
Phishing is more advanced than ever, and that’s where natural language processing shines.
Research shows that integrating NLP and machine learning for phishing detection can achieve classification accuracy as high as 97.98 %.
- Analyzes emails and messages for manipulative language or malicious links
- Detects impersonation attempts and deceptive requests targeting human resources
- Filters out spear phishing attacks using tone and intent analysis
- Integrates with email gateways for real-time response
- Assists cybersecurity professionals in reviewing flagged content efficiently
What Are the Most Effective AI Applications in Cybersecurity?
We’ve seen how AI detects threats, but how is it helping real teams solve real security problems every day? The beauty of AI in cybersecurity lies in its flexibility. Whether you're protecting personal devices, managing massive networks, or navigating the cloud, AI is there to support, scale, and strengthen your defense.
AI in Cybersecurity: Benefits, Risks, and Strategies; 73 % of organizations use AI for core security activities
This section breaks down the top areas where AI-powered cybersecurity solutions are having a significant impact. These aren’t just buzzwords; these are practical tools that help security professionals work faster, smarter, and with more confidence.
AI in Endpoint Security and Access Control
Endpoints are often where attackers strike first. With AI, you can lock them down before anything slips through the cracks.
A 2025 survey found that 73 % of organizations believe AI improves their ability to detect new threats and are already implementing AI‑driven endpoint security solutions. Showing AI is becoming a fundamental part of modern cybersecurity strategies.
| What It Protects | How AI Helps |
|---|---|
| Devices & Login Sessions | Flags risky logins and strange device behavior in real time |
| Sensitive User Accounts | Uses behavior-based detection to stop unauthorized access attempts |
| Access Management Systems | Integrates with IAM tools to apply smarter, context-based rules |
| Security Team Efficiency | Automates routine device checks and reduces alert fatigue |
| Company Data | Helps secure every access point before it becomes a weak spot |
Why it matters: AI doesn’t sleep, and with endpoints, that’s exactly what you need—constant, intelligent surveillance.
AI for Vulnerability Scanning and Patch Management
Still relying on monthly patch cycles? That’s like checking your locks once a year. AI helps you find and fix weak points before hackers do.
Organizations using AI‑powered vulnerability scanning and risk prioritization have seen up to 60 – 80 % reductions in false positives. Making it far easier for teams to focus on real issues rather than chasing endless non‑issues.
| Challenge | How AI Solves It |
|---|---|
| Missed Vulnerabilities | Scans continuously to detect even subtle flaws |
| Too Many Patches, Not Enough Time | Prioritizes based on potential threats and real-world risk levels |
| Downtime Concerns | Schedules patches at ideal times to avoid workflow interruptions |
| Alert Overload | Cuts through the noise and focuses your attention |
| Team Bandwidth | Supports security operations with automation, not more workload |
Why it matters: With AI, patching isn’t just faster—it’s smarter, more targeted, and easier to manage.
Predictive Analytics for Threat Intelligence
What if your system could predict the next attack? AI makes that a reality by analyzing huge amounts of threat data to spot risks before they hit.
Predictive threat intelligence shifts cybersecurity from reactive to proactive, letting teams anticipate and disrupt emerging threats.
| Intelligence Area | AI Capability |
|---|---|
| Global Threat Monitoring | Tracks emerging threats and alerts teams early |
| Attack Pattern Recognition | Identifies suspicious behaviors based on historical data |
| Risk Scoring | Assigns threat levels to help teams prioritize responses |
| Human Analyst Support | Reduces manual digging with fast, accurate recommendations |
| Strategy Development | Helps teams stay ahead and refine their future defense plans |
Why it matters: This is where AI shines; it’s not just reactive, it’s strategically predictive.
AI-Powered Incident Response and Recovery
The faster you act during a cyber attack, the less damage it causes. AI helps your team respond like clockwork, not chaos.
Organizations that use AI and automation in their incident response workflows can reduce breach containment time by up to 40 % compared to manual processes, enabling quicker recovery and minimizing damage.
| Crisis Scenario | AI Response |
|---|---|
| Active Threat Detected | Immediately isolates infected systems |
| Confusion in Response Steps | Executes predefined playbooks and recovery protocols |
| Human Error Risks | Guides teams with AI-powered insights and suggested actions |
| Post-Attack Analysis | Investigate how the breach happened using machine learning |
| Recovery Time Concerns | Speeds up return to normal with automated recovery steps |
Why it matters: AI reduces panic time. It gives your team a clear, fast path forward when every second counts.
Cloud and Network Security Using AI
Modern infrastructure means modern threats. Whether you're running on AWS, Azure, or a hybrid setup, AI helps you keep it all secure.
Organizations leveraging AI for cloud threat detection and policy enforcement can spot unauthorized access and configuration changes in real time. Significantly improving overall defense posture and reducing the window of vulnerability when attackers strike.
| Cloud/Network Element | AI Solution |
|---|---|
| Unusual Network Activity | Tracks and flags strange network traffic in real time |
| Cloud Misconfigurations | Detects policy gaps or risky permissions before they’re exploited |
| Cross-Platform Visibility | Offers a unified view across all environments |
| Insider Threats in Cloud Apps | Monitors user behavior to spot misuse in cloud systems |
| Growth at Scale | Uses AI capabilities to handle expanding workloads effortlessly |
Why it matters: Cloud security needs to move as fast as your business—and AI is built to keep up.
How AI Enhances Business Cybersecurity Strategy
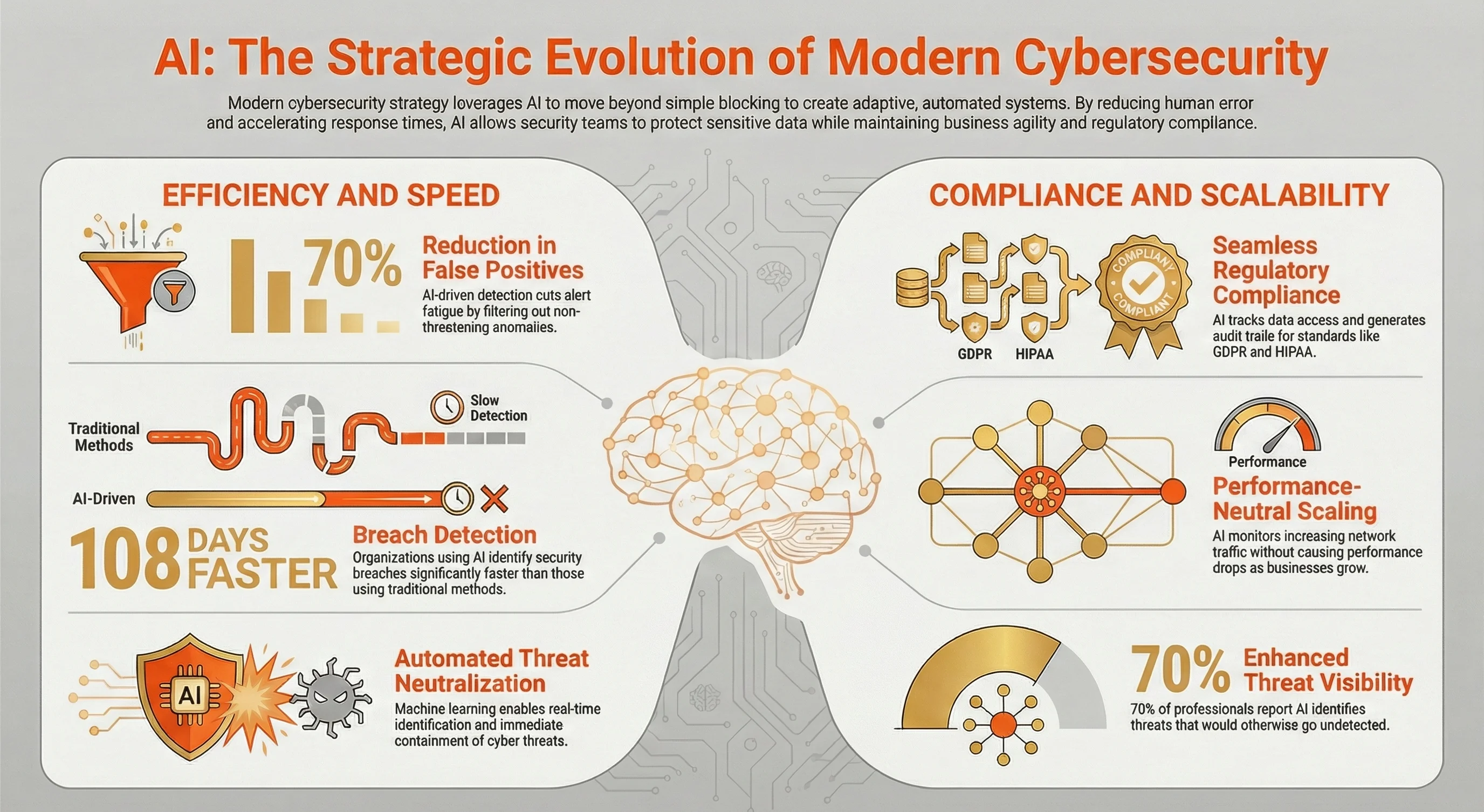
A strong cybersecurity strategy today isn't just about blocking attacks—it's about building systems that adapt, scale, and protect sensitive data without slowing the business down. This is where AI in cybersecurity transforms from a tool into a strategic asset. From reducing costly mistakes to supporting compliance and scalability, AI empowers security teams to work smarter and more effectively.
According to a Ponemon Institute study, 70 % of cybersecurity professionals say AI is highly effective at identifying threats. that would otherwise go undetected, underscoring AI’s strategic value in emerging defense models.
Reducing Human Error Through Automation
Manual tasks can lead to missed alerts, misconfigurations, or delayed responses, especially in fast-moving environments.
Gartner reportsGartner reports that organizations using AI‑driven detection systems can cut false positives by up to 70%, significantly reducing human error and alert fatigue in threat detection workflows.
- AI automates repetitive security tasks such as scanning security logs, analyzing anomalies, and flagging potential threats.
- AI-powered systems reduce dependence on human analysts, lowering the risk of fatigue-related oversight.
- Automated decision-making strengthens overall security posture without compromising agility.
Improving Response Time and Accuracy
When cyber attacks happen, seconds matter. AI helps teams act fast and precisely.
- Real-time threat detection, supported by machine learning, ensures that threats are identified and neutralized quickly.
- AI reduces false positives, improving efficiency for cybersecurity professionals.
- Enhanced pattern recognition allows AI to identify vulnerabilities that human eyes may miss.
According to industry research, organizations with AI‑powered cybersecurity solutions identify breaches on average 108 days faster than those using traditional methods
AI in Regulatory Compliance and Data Privacy
Regulations around data security are tightening. AI assists businesses in staying compliant.
- Tracks how sensitive data is accessed and used across systems
- Supports security measures aligned with standards like GDPR or HIPAA
- Provides audit trails, simplifying compliance reporting
Nearly 40 % of organizations have reported privacy‑related incidents involving AI systems, highlighting the need for strong AI‑enabled data governance and compliance monitoring to prevent breaches and regulatory fallout.
Scalable AI Security Solutions for Growing Businesses
As businesses expand, so do their risks. AI scales effortlessly.
- Monitors increasing network traffic without performance drops
- Integrates with cloud and hybrid environments to protect critical data
- Offers adaptive cybersecurity solutions that grow with your infrastructure
AI cybersecurity solutions are inherently scalable, allowing both small and large organizations to monitor network traffic and threats without performance drops as workloads increase.
What Are the Current Limitations and Challenges of AI in Cybersecurity?
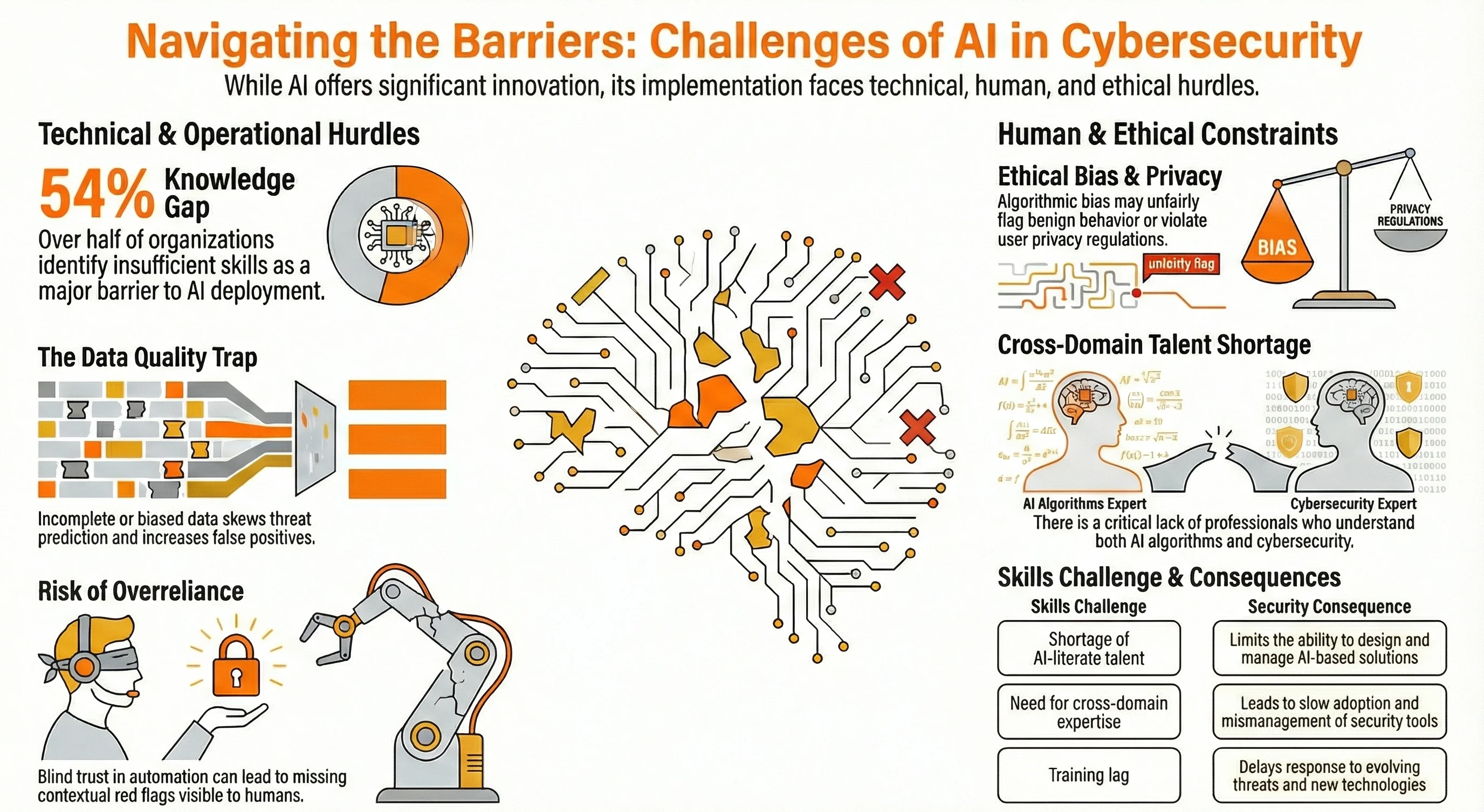
While AI in cybersecurity brings undeniable power and innovation, it’s not without its hurdles. Organizations often discover that implementing AI technologies is not as simple as flipping a switch.
A recent Global Cybersecurity Outlook survey found that 54 % of organizations identify insufficient knowledge or skills as a significant barrier to deploying AI in cybersecurity
From data issues to talent shortages, businesses face practical and ethical challenges when adopting AI-powered cybersecurity solutions. It’s essential to understand these limitations—not to avoid AI, but to prepare for smarter implementation.
Below, we break down the most pressing challenges holding back the full potential of AI systems in the security world.
What Does the Future Hold for AI in Cybersecurity?
As threats become more sophisticated, so must the tools we use to fight them. The future of AI in cybersecurity is not just about reacting faster; it’s about anticipating attacks, scaling protection, and reshaping how we defend our digital environments.
With the rise of generative AI, interconnected devices, and more innovative AI-powered systems, cybersecurity is evolving into a more predictive, adaptive, and autonomous force.
So, what’s next?
Generative AI and the Next Evolution of Cyber Defense
Generative AI is set to change both sides of the cybersecurity equation for defenders and attackers.
- Can create dynamic security simulations for proactive threat hunting
- Enhances automated analysis of security logs and incident scenarios
- May also be exploited by malicious actors to craft smarter phishing campaigns
- Requires constant updates to stay ahead of evolving threats
AI‑driven cyberattacks are on the rise, with deepfake‑based attacks projected to increase by 50 – 60% in 2024, producing up to 140,000–150,000 incidents globally
How AI Will Tackle Emerging Threats
AI’s future lies in its ability to adapt faster than attackers evolve.
- Learns from historical data to anticipate new cyber threats
- Integrates global threat intelligence to detect trends earlier
- Improves pattern recognition to identify evolving threats in real time
- Supports security teams with faster alerts and less noise
AI‑Driven Security Systems Can Anticipate Emerging Threats and Detect Abnormal Behavior
Future Use Cases in IoT, Blockchain, and Smart Systems
As tech environments grow, so will AI’s footprint in keeping them secure.
- Monitors network traffic and anomalies in smart devices
- Detects fraud and vulnerabilities in blockchain transactions
- Enables cybersecurity solutions for edge computing and embedded systems
- Uses AI capabilities to scale across massive, decentralized ecosystems
Research shows AI combined with blockchain can improve threat detection and resistance against attacks in IoT ecosystems, increasing data integrity and privacy safeguards
Will AI Replace Human Cybersecurity Experts?
Not likely—but it will change their roles.
- AI reduces manual load, but still needs human oversight
- Complex security incidents often require human context and ethics
- Collaboration between AI tools and cybersecurity professionals is the key
- The future is hybrid: AI as an enabler, humans as the decision-makers
AI paired with blockchain can help secure authentication and tamper‑proof records for massive decentralized device networks, addressing scale and trust issues absent in traditional systems.
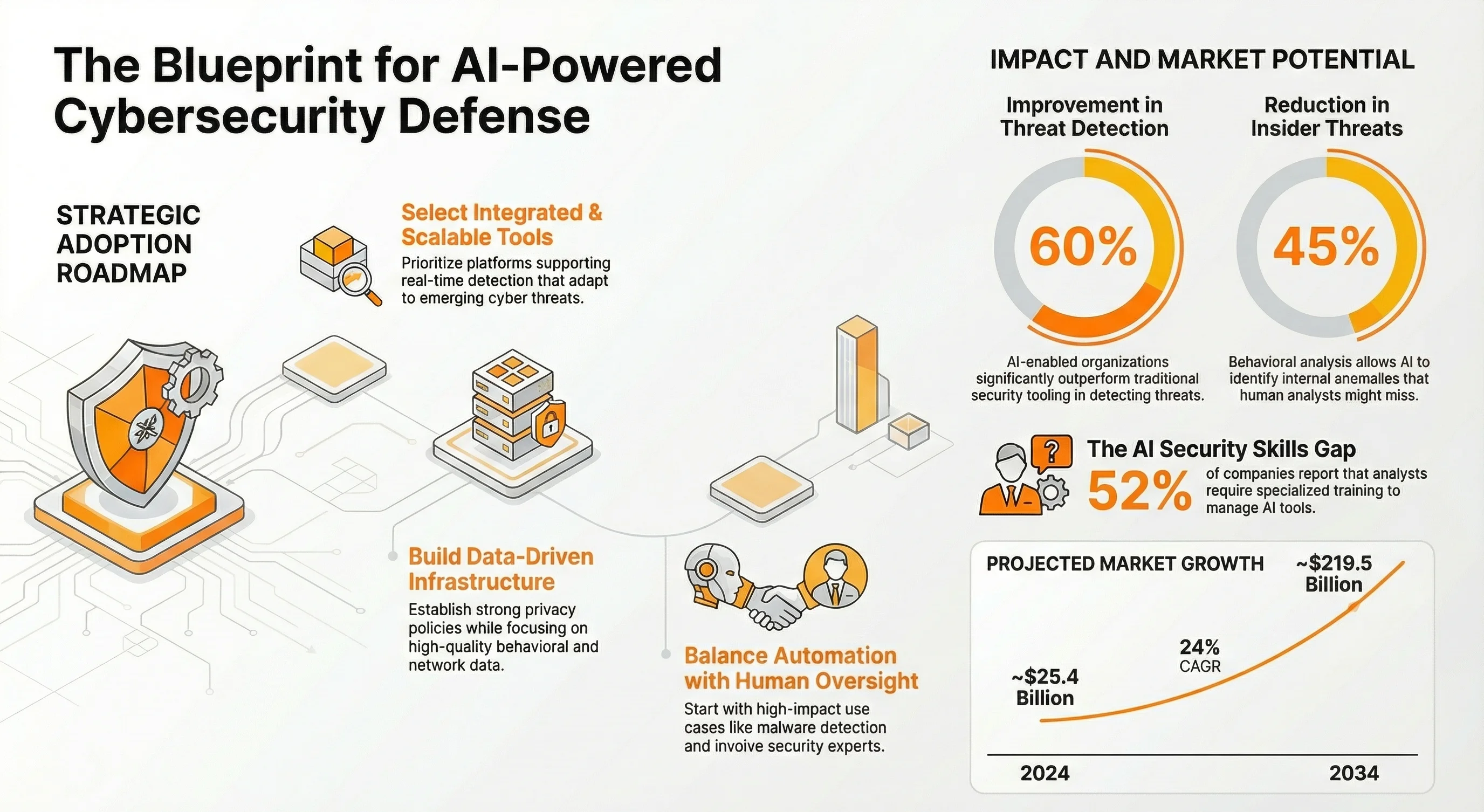
Getting Started: How Can Your Business Adopt AI for Cybersecurity?
Ready to put AI in cybersecurity to work for your business? Getting started doesn’t require a massive overhaul—just smart planning and the right tools. Whether you're protecting sensitive customer data or scaling your security operations, AI can give your team a significant edge if implemented strategically.
The AI in cybersecurity market was valued at ~$25.4 billion in 2024 and is projected to grow to ~$219.5 billion by 2034 — a CAGR of around 24%.
Here are the steps you need to take:
1. Choosing the Right AI Tools and Platforms
- Look for platforms that support real-time threat detection and automated response
- Ensure integration with existing security tools and systems
- Prioritize solutions that scale with your business and adapt to emerging threats
Organizations with AI‑security tools report up to 60% improved threat detection compared to traditional tooling.
2. Building a Data-Driven Security Infrastructure
- Focus on high-quality, diverse data sources for training your AI models
- Establish strong data security and privacy policies
- Ensure infrastructure supports the storage and analysis of network traffic and behavioral data
AI can reduce insider threats by about 45% by analyzing user behavior for anomalies.
3. Best Practices for Implementing AI in Cybersecurity
- Start small with high-impact use cases like malware and phishing detection
- Involve both security professionals and data experts for balanced execution
- Combine automation with human intervention to maintain control and trust
About 52% of companies say analysts need training to effectively manage AI security tools.
4. Measuring the ROI of AI-Powered Security Systems
- Track improvements in response time, false positives, and resource efficiency
- Evaluate how well AI helps protect sensitive data and reduce cyber risks
- Align outcomes with broader business goals like compliance, uptime, and customer trust
Conclusion
The world of cybersecurity is evolving rapidly, and AI is no longer a futuristic concept—it’s a present-day necessity. From stopping threats in real time to predicting future attacks before they happen, AI in cybersecurity offers organizations the speed, intelligence, and adaptability they need to stay secure in an increasingly complex digital world.
But as powerful as AI is, success lies in how you use it. Choosing the right tools, aligning them with your business goals, and ensuring human oversight are critical steps in building a smart, resilient defense strategy. Whether you're just getting started or refining your current systems, embracing AI today means safeguarding your future.
At AIChief, we’re passionate about breaking down the complex world of AI into practical, actionable insights. If you're looking to stay ahead of cyber threats, scale your protection, and lead with confidence, you're in the right place.
FAQs
Emily Newton
Emily Newton is an experienced Editor-in-Chief who has spent the last decade sharing her insights on science and technology advances through platforms like IoT for All and DZone. She is deeply interested in showcasing how connected technologies and smart ecosystems transform modern businesses. When she isn’t writing, Emily enjoys walking local trails, playing video games, or curling up with a good book.